Following a short consultation period, the Office of the Superintendent of Financial Institutions ("OSFI") released its final Integrity and Security Guideline ("I&S Guideline") on Jan. 31, 2024. This new guidance from OSFI focuses on federally regulated financial institutions' ("FRFIs") acting with integrity and securing themselves against diverse threats, including foreign interference.
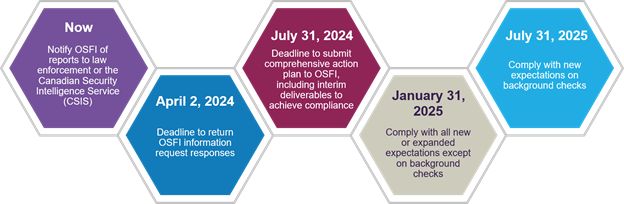
The key dates and deliverables under the I&S Guideline are as follows:
The I&S Guideline applies to: banks, cooperative credit associations, foreign bank branches, foreign insurance branches, life insurance and fraternal insurance companies, property and casualty insurance companies and trust and loan companies. The I&S Guideline applies to foreign branches of banks and insurers to the extent that it is relevant to their ability to meet applicable requirements and legal obligations in Canada.
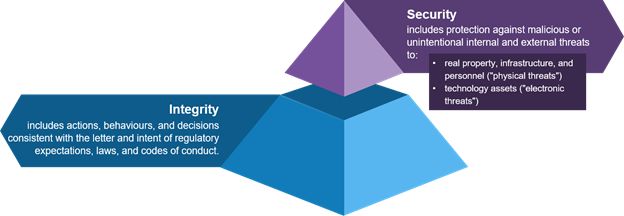
Integrity and security
Integrity and security are outcomes of separate risk management practices, but are related in that acting with integrity can enhance a FRFI's security.
OSFI will soon require regulated FRFIs to establish, implement, maintain and adhere to adequate policies and procedures to protect against threats to integrity or security.
The I&S Guideline has a specific approach to proportionality. OSFI will apply the I&S Guideline on a proportional basis assessed with reference to the FRFI's: ownership structure, strategy and risk profile and scope, nature and location of operations.
Outcomes and principles
The I&S Guideline is organized around two expected outcomes, each with supporting principles that are designed to increase the likelihood of the outcomes.
1. Integrity
|
Outcome: Actions, behaviours, and decisions are consistent with the letter and intent of regulatory expectations, laws, and codes of conduct. |
||
|
Topic |
Principle |
Summary |
|
Character |
Principle 1: Responsible persons and leaders are of good character and demonstrate integrity through their actions, behaviours, and decisions. |
The importance of good character and integrity are directly proportional to the power and influence a person has within an organization. |
|
Culture |
Principle 2: Culture that demonstrates integrity is deliberately shaped, evaluated, and maintained. |
Cultures are variable across organizations, but all cultures should reflect a commitment to norms that encourage ethical behaviour. What is considered acceptable and unacceptable within an organization should be deliberately shaped, evaluated and maintained. |
|
Governance |
Principle 3: Governance structures subject actions, behaviours, and decisions to appropriate scrutiny and challenge. |
Sound governance involves scrutinizing and challenging actions, behaviours, and decisions, and building trust with stakeholders. It also requires effective oversight of senior management, clear communication of expectations, and regular monitoring of compliance with codes of conduct. |
|
Compliance |
Principle 4: Effective mechanisms to identify and verify compliance with regulatory expectations, laws, and codes of conduct exist. |
Compliance risk management is a vital aspect of integrity. An enterprise-wide regulatory compliance management (RCM) framework is an essential tool for this purpose. It should address actions, behaviours, and decisions against compliance requirements and include internal and external channels in which concerns can be raised. |
2. Security
|
Outcome: Operations, physical premises, people, technology assets, and data and information are resilient and protected against threats. |
||
|
Topic |
Principle |
Summary |
|
Physical premises |
Principle 5: Physical premises are safe and secure and monitored appropriately. |
Standards and controls commensurate with the threat environment should govern physical and digital assets. These should be supported by technical security inspections including for covert surveillance, listening, or tracking devices. |
|
People |
Principle 6: People should be subject to appropriate background checks, and strategies should be put in place to manage risk. |
Standards and controls should be established and maintained to protect people from undue influence, foreign interference, and malicious activity. Appropriate background checks are a key tool for this purpose, provided that they are risk-based. Factors such as authority, seniority, and access to sensitive information should be considered. |
|
Technology assets |
Principle 7: Technology assets should be secure, with weaknesses identified and addressed, effective defences in place, and issues identified accurately and promptly. |
The vulnerability of technology assets can pose both financial and non-financial risks to FRFIs. FRFIs should develop controls for technology assets that are proportional to the likelihood of threats and the severity of impact to the FRFI's employees, clients, and other stakeholders should the technology asset be compromised. |
|
Data and information |
Principle 8: Data and information should be subject to appropriate standards and controls ensuring its confidentiality, integrity, and availability. |
Maintaining data security is imperative and requires controls and protections throughout the data lifecycle, considering the data's sensitivity and vulnerability. Data should be identified, classified and protected based on employee access requirements. Data classification should also consider vulnerability to malicious activity and undue influence or foreign interference. The FRFI's defences should match the threat level and potential harm caused by a breach to the FRFI and the FRFI's employees, clients and other stakeholders. |
|
Third-party risks |
Principle 9: Third parties should be subject to equivalent and proportional measures to protect against threats. |
FRFIs are accountable for their security as it relates to third parties providing outsourced services. FRFIs should engage in due diligence, a proportionality assessment, and initial and ongoing security assessments with respect to both third parties and their subcontractors. |
|
Undue influence, foreign interference, and malicious activity |
Principle 10: Threats stemming from suspected undue influence, foreign interference, and malicious activity should be promptly detected and reported. |
If a FRFI reports a threat to the appropriate authorities, including CSIS and the Royal Canadian Mounted Police, OSFI should also be informed immediately. Controls should be established to detect threats and processes should be established for their careful investigation. Whether or not they are subject to reporting, detected incidents and events should be documented, inventoried and reported to senior management. |
Focus on national security in the financial sector
This new OSFI guideline is part of the Canadian federal government's recent focus on national security in the financial sector. In connection with Budget 2023, Parliament expanded OSFI's mandate in its governing legislation and the statutes governing FRFIs. This expanded mandate includes OSFI's supervision of FRFIs in order to determine whether they have adequate policies and procedures to protect themselves against threats to their integrity or security. These legislative changes came into force on Jan.1, 2024 and the I&S Guideline is intended to set out OSFI's expectations in this area to support OSFI's expanded mandate.
Many of the new expectations in the I&S Guideline focus on the risks of undue influence, foreign interference and malicious activity to FRFIs. For the purposes of the I&S Guideline, OSFI has defined those terms as follows:
- "Undue influence" includes situations where a person or entity engages, with malicious intent, in actions, behaviours, deception or the use of power to impact actions, decisions, or behaviours in their own or another's interests. Undue influence can originate from foreign or domestic actors and may have national security implications.
- "Foreign interference" includes activities that are within or relating to Canada, detrimental to the interests and security of Canada, and are clandestine or deceptive or involve a threat to any person, including attempts to covertly influence, intimidate, manipulate, interfere, corrupt, or discredit individuals, organizations, and governments to further the interests of a foreign state-or-non-state actor.
- "Malicious activity" includes actions taken with the intent of causing harm including theft, coercion, fraud, manipulation of information or disruptions that are otherwise illegal, malicious, clandestine, or deceptive in nature. Malicious activity can originate from foreign or domestic actors and may have national security implications.
Despite referring to these concepts generally, many questions remain about how OSFI will assess the risks of undue influence, foreign interference or malicious activity in practice. FRFIs should consider carefully how to implement these new expectations into their practices and procedures and what liability might arise from the actions they take in this regard.
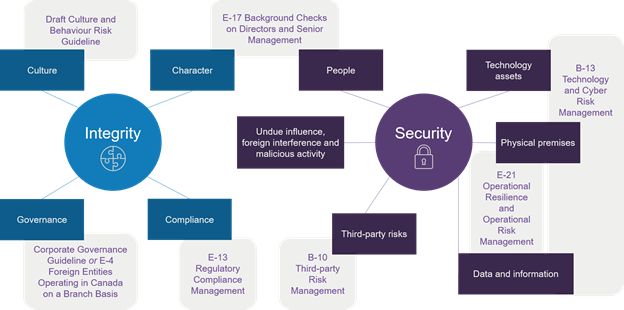
Interaction with existing OSFI guidance
The outcomes and principles articulated in the I&S Guideline directly and indirectly engage existing OSFI guidelines. The Appendix to the I&S Guideline helpfully summarizes the new and expanded expectations with reference to the relevant existing and draft OSFI guidelines. As OSFI reviews and updates its guidelines, we expect some of the new expectations in the I&S Guideline to be incorporated into existing guidelines. The current interaction between the concepts in the I&S Guideline and existing and draft OSFI guidelines can be depicted as follows:
Read the original article on GowlingWLG.com
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.


